WPA2 : AP-STA between 2 Linux laptops
Step 1: STA : Remove old packages |
Step 1: AP : Remove old packages |
$ cd $HOME
$ rm -rf hostap* wpa_supp*
|
$ cd $HOME
$ rm -rf hostap* wpa_supp*
|
Step 2: STA : Download wpa_supplicant |
Step 2: AP : Download hostapd |
Note Make sure internet is available in laptop to download supplicant package |
Note Make sure internet is available in laptop to download hostapd package |
$ sudo wget https://w1.fi/releases/wpa_supplicant-2.9.tar.gz
|
$ sudo wget http://w1.fi/releases/hostapd-2.9.tar.gz
|
Step 3: STA : Install libraries |
Step 3: AP : Install libraries |
Note Make sure internet is available in laptop to download libraries |
Note Make sure internet is available in laptop to download libraries |
$ sudo apt install libnl-genl-3-dev libnl-3-dev libdbus-glib-1-dev
|
$ sudo apt install libnl-genl-3-dev libnl-3-dev libdbus-glib-1-dev
|
Step 4: STA : Stop ongoing wireless activities |
Step 4: AP : Stop ongoing wireless activities |
Warning Internet is cut-off after this ! |
Warning Internet is cut-off after this ! |
$ sudo killall wpa_supplicant
$ sudo killall wpa_cli
$ sudo killall hostapd
$ sudo killall hostapd_cli
$ sudo /etc/init.d/network-manager stop
Stopping network-manager (via systemctl): network-manager.service.
$ sudo rfkill list all
0: hci0: Bluetooth
Soft blocked: no
Hard blocked: no
1: dell-wifi: Wireless LAN
Soft blocked: no
Hard blocked: no
2: dell-bluetooth: Bluetooth
Soft blocked: no
Hard blocked: no
3: phy0: Wireless LAN
Soft blocked: no
Hard blocked: no
4: phy1: Wireless LAN
Soft blocked: no
Hard blocked: no
5: phy2: Wireless LAN
Soft blocked: no
Hard blocked: no
$ sudo rfkill unblock all
$ sudo ifconfig wlan1 up
|
$ sudo killall wpa_supplicant
$ sudo killall wpa_cli
$ sudo killall hostapd
$ sudo killall hostapd_cli
$ sudo killall dhclient
$ sudo /etc/init.d/network-manager stop
Stopping network-manager (via systemctl): network-manager.service.
$ sudo rfkill list all
0: hci0: Bluetooth
Soft blocked: no
Hard blocked: no
1: dell-wifi: Wireless LAN
Soft blocked: no
Hard blocked: no
2: dell-bluetooth: Bluetooth
Soft blocked: no
Hard blocked: no
3: phy0: Wireless LAN
Soft blocked: no
Hard blocked: no
4: phy1: Wireless LAN
Soft blocked: no
Hard blocked: no
5: phy2: Wireless LAN
Soft blocked: no
Hard blocked: no
$ sudo rfkill unblock all
$ sudo ifconfig wlan0 up
|
Step 5: STA : Wireless interface status before connection |
Step 5: AP : Wireless interface status before connection |
Note wlan1 is the name of wireless interface on this laptop |
Note wlan0 is the name of wireless interface on this laptop |
$ sudo iwconfig wlan1
wlan1 IEEE 802.11 ESSID:off/any
Mode:Managed Access Point: Not-Associated Tx-Power=20 dBm
Retry short limit:7 RTS thr:off Fragment thr:off
Power Management:on
|
$ sudo iwconfig wlan0
wlan0 IEEE 802.11 ESSID:off/any
Mode:Managed Access Point: Not-Associated Tx-Power=20 dBm
Retry short limit:7 RTS thr:off Fragment thr:off
Power Management:on
|
Step 6: STA : ifconfig interface status before connection |
Step 6: AP : ifconfig interface status before connection |
$ sudo ifconfig wlan1
wlan1: flags=4099<UP,BROADCAST,MULTICAST> mtu 1500
ether 02:00:00:00:01:00 txqueuelen 1000 (Ethernet)
RX packets 0 bytes 0 (0.0 B)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 0 bytes 0 (0.0 B)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
|
$ sudo ifconfig wlan0
wlan0: flags=4099<UP,BROADCAST,MULTICAST> mtu 1500
ether 02:00:00:00:00:00 txqueuelen 1000 (Ethernet)
RX packets 0 bytes 0 (0.0 B)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 0 bytes 0 (0.0 B)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
|
Step 7: STA : Extract wpa_supplicant |
Step 7: AP : Extract hostapd |
Note tar -xvf command extracts zipped supplicant package |
Note tar -xvf command extracts zipped hostapd package |
$ sudo tar -xvf wpa_supplicant-2.9.tar.gz
|
$ sudo tar -xzvf hostapd-2.9.tar.gz
|
Step 8: STA : Compile wpa_supplicant |
Step 8: AP : Compile hostapd |
Note .config file is required for make to start compilation of supplicant |
Note .config file is required for make to start compilation of hostapd |
$ cd wpa_supplicant-2.9/wpa_supplicant
$ cp defconfig .config
$ make
|
$ cd hostapd-2.9/hostapd
$ cp defconfig .config
$ make
|
Step 9: STA : Create run_supplicant.conf |
Step 9: AP : Create run_hostapd.conf |
Note ssid in ./run_supplicant.conf should match ssid in ./run_hostapd.conf |
Note ssid in ./run_hostapd.conf should be used by clients while connecting to AP |
$ sudo vim ./run_supplicant.conf
ctrl_interface=/run/wpa_supplicant
update_config=1
network={
ssid="test_wpa2"
proto=WPA2
key_mgmt=WPA-PSK
psk="12345678"
}
|
$ sudo vim ./run_hostapd.conf
ctrl_interface=/run/hostapd
interface=wlan0
driver=nl80211
ssid=test_wpa2
hw_mode=g
channel=6
macaddr_acl=0
auth_algs=1
ignore_broadcast_ssid=0
wpa=2
wpa_passphrase=12345678
wpa_key_mgmt=WPA-PSK
rsn_pairwise=CCMP
group_cipher=CCMP
|
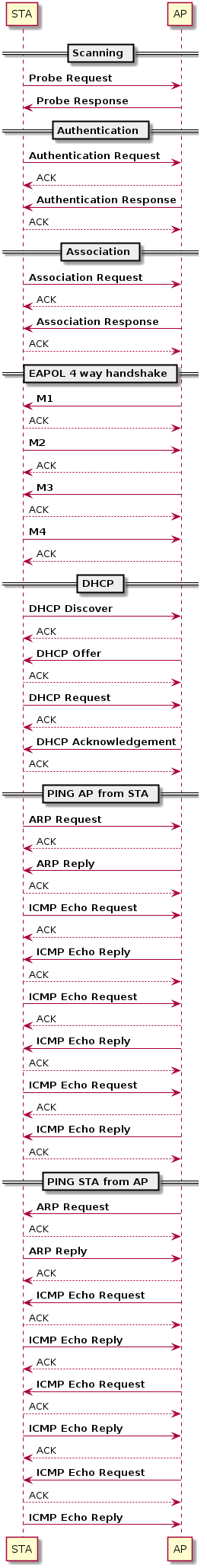
MONITOR : Let us start Sniffer to capture all packets between STA and AP |
|
$ sudo iw dev wlan1 interface add moni0 type monitor
$ sudo iw dev moni0 set type monitor
$ sudo ifconfig moni0 up
$ sudo iw dev moni0 set channel 6
$ sudo iwconfig moni0
wlan3 IEEE 802.11 Mode:Monitor Frequency:2.437 GHz Tx-Power=20 dBm
Retry short limit:7 RTS thr:off Fragment thr:off
Power Management:on
$ sudo iw dev
phy#4
Interface moni0
ifindex 7
wdev 0x400000001
addr 02:00:00:00:03:00
type monitor
channel 6 (2437 MHz), width: 20 MHz (no HT), center1: 2437 MHz
txpower 20.00 dBm
$ sudo apt-get install wireshark
$ sudo wireshark
|
|
Step 10: STA : Run wpa_supplicant |
Step 10: AP : Run hostapd |
Note CTRL-EVENT-CONNECTED indicates successful connection to AP |
Note AP-STA-CONNECTED indicates successful connection of STA |
$ sudo ./wpa_supplicant -Dnl80211 -i wlan1 -c ./run_supplicant.conf
Successfully initialized wpa_supplicant
wlan1: SME: Trying to authenticate with 02:00:00:00:00:00 (SSID='test_wpa2' freq=2437 MHz)
wlan1: Trying to associate with 02:00:00:00:00:00 (SSID='test_wpa2' freq=2437 MHz)
wlan1: Associated with 02:00:00:00:00:00
wlan1: CTRL-EVENT-SUBNET-STATUS-UPDATE status=0
wlan1: WPA: Key negotiation completed with 02:00:00:00:00:00 [PTK=CCMP GTK=CCMP]
wlan1: CTRL-EVENT-CONNECTED - Connection to 02:00:00:00:00:00 completed [id=0 id_str=]
|
$ sudo ./hostapd ./run_hostapd.conf
Configuration file: /etc/hostapd/hostapd.conf
Using interface wlan0 with hwaddr 02:00:00:00:00:00 and ssid "test_wpa2"
wlan0: interface state UNINITIALIZED->ENABLED
wlan0: AP-ENABLED
|
Step 11: STA : Check ps status and confirm wpa_supplicant process is running |
Step 11: AP : Check ps status and confirm hostapd process is running |
$ ps -N | grep -i wpa
36164 pts/2 00:00:00 wpa_supplicant
|
$ ps -N | grep -i hostapd
36261 pts/3 00:00:00 hostapd
|
Step 12: STA : Check connection status using wpa_cli |
Step 12: AP : Check connection status using hostapd_cli |
Note wpa_state=COMPLETED indicates successful connection. Check output of status |
Note aid=1 is assigned to connected station. Check output of all_sta |
$ sudo ./wpa_cli -i wlan1
> status
bssid=02:00:00:00:00:00
freq=2437
ssid=test_wpa2
id=0
mode=station
pairwise_cipher=CCMP
group_cipher=CCMP
key_mgmt=WPA2-PSK
wpa_state=COMPLETED
address=02:00:00:00:01:00
uuid=572cf82f-c957-5653-9b16-b5cfb298abf1
$ sudo ./wpa_cli -i wlan1
> scan
OK
<3>CTRL-EVENT-SCAN-STARTED
<3>CTRL-EVENT-SCAN-RESULTS
>
> scan_result
bssid / frequency / signal level / flags / ssid
02:00:00:00:00:00 2437 -30 [WPA2-PSK-CCMP][ESS] test_wpa2
>
> add_network
0
> set_network 0 ssid "test_wpa2"
OK
<3>CTRL-EVENT-SCAN-STARTED
set_network 0 key_mgmt WPA-PSK
> OK
<3>CTRL-EVENT-SCAN-RESULTS
set_network 0 proto WPA2
> OK
> set_network 0 psk "12345678"
OK
> enable_network 0
OK
<3>CTRL-EVENT-SCAN-STARTED
>
<3>CTRL-EVENT-SCAN-RESULTS
<3>SME: Trying to authenticate with 02:00:00:00:00:00 (SSID='test_wpa2' freq=2437 MHz)
<3>Trying to associate with 02:00:00:00:00:00 (SSID='test_wpa2' freq=2437 MHz)
<3>Associated with 02:00:00:00:00:00
<3>CTRL-EVENT-SUBNET-STATUS-UPDATE status=0
<3>WPA: Key negotiation completed with 02:00:00:00:00:00 [PTK=CCMP GTK=CCMP]
<3>CTRL-EVENT-CONNECTED - Connection to 02:00:00:00:00:00 completed [id=0 id_str=]
<3>CTRL-EVENT-SCAN-STARTED
>
> status
bssid=02:00:00:00:00:00
freq=2437
ssid=test_wpa2
id=0
mode=station
pairwise_cipher=CCMP
group_cipher=CCMP
key_mgmt=WPA2-PSK
wpa_state=COMPLETED
address=02:00:00:00:01:00
uuid=572cf82f-c957-5653-9b16-b5cfb298abf1
|
$ sudo ./hostapd_cli -i wlan0
hostapd_cli v2.9
Copyright (c) 2004-2019, Jouni Malinen <j@w1.fi> and contributors
This software may be distributed under the terms of the BSD license.
See README for more details.
Interactive mode
|
Step 13: STA : Wireless interface status after connection |
Step 13: AP : Wireless interface status after connection |
Note ESSID field in iwconfig should show ssid of AccessPoint |
Note Mode field in iwconfig should show master |
$ sudo iwconfig
wlan1 IEEE 802.11 ESSID:"test_wpa2"
Mode:Managed Frequency:2.437 GHz Access Point: 02:00:00:00:00:00
Bit Rate:54 Mb/s Tx-Power=20 dBm
Retry short limit:7 RTS thr:off Fragment thr:off
Power Management:on
Link Quality=70/70 Signal level=-30 dBm
Rx invalid nwid:0 Rx invalid crypt:0 Rx invalid frag:0
Tx excessive retries:0 Invalid misc:0 Missed beacon:0
$ sudo iw dev
phy#2
Interface wlan1
ifindex 6
wdev 0x200000001
addr 02:00:00:00:01:00
ssid test_wpa2
type managed
channel 6 (2437 MHz), width: 20 MHz (no HT), center1: 2437 MHz
|
$ sudo iwconfig
wlan0 IEEE 802.11 Mode:Master Tx-Power=20 dBm
Retry short limit:7 RTS thr:off Fragment thr:off
Power Management:on
$ sudo iw dev
phy#1
Interface wlan0
ifindex 5
wdev 0x100000001
addr 02:00:00:00:00:00
ssid test_wpa2
type AP
channel 6 (2437 MHz), width: 20 MHz (no HT), center1: 2437 MHz
txpower 20.00 dBm
|
Step 14: STA : Assign Static IP address |
Step 14: AP : Assign Static IP address |
Note Station and AP should be in same IP subnet. Assign 192.168.3.10 to Station |
Note Station and AP should be in same IP subnet. Assign 192.168.3.1 to AP |
Attention Use static IP assignment if DHCP server is not supported by AP |
Attention Use static IP assignment if DHCP server is not supported by AP |
$ sudo ifconfig wlan1 192.168.3.10 up
$ sudo ifconfig wlan1
wlan1: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.3.10 netmask 255.255.255.0 broadcast 192.168.3.255
ether 02:00:00:00:01:00 txqueuelen 1000 (Ethernet)
RX packets 73 bytes 13119 (13.1 KB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 65 bytes 13111 (13.1 KB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
|
$ sudo ifconfig wlan0 192.168.3.1 up
$ sudo ifconfig wlan0
wlan0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.3.1 netmask 255.255.255.0 broadcast 192.168.3.255
ether 02:00:00:00:00:00 txqueuelen 1000 (Ethernet)
RX packets 61 bytes 11085 (11.0 KB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 130 bytes 25688 (25.6 KB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
|
Step 15: STA : Assign DHCP IP address |
Step 15: AP : Assign DHCP IP address |
Attention This initiates DORA. Make sure DHCP server is running in AP ! |
Attention isc-dhcp-server needs to be installed to setup DHCP server |
Note dhclient is DHCP client |
Note See below ! Add configuration in /etc/dhcp/dhcpd.conf |
Note dhclient -r releases existing IP |
Note See below ! Add configuration in /etc/network/interfaces |
Note dhclient -i wlan1 gets IP address from DHCP server |
Note See below ! Add configuration in /etc/default/isc-dhcp-server |
# Release any existing IP address
$ sudo dhclient -r
$ sudo ifconfig wlan1 0.0.0.0 up
# Run DHCP client on wlan1. This initiates DORA
$ sudo dhclient -i wlan1
# Check if wlan1 got IP address
$ sudo ifconfig wlan1
|
Setup DHCP server : https://help.ubuntu.com/community/isc-dhcp-server
$ sudo dpkg --configure -a
$ sudo apt-get install isc-dhcp-server
$ sudo vim /etc/dhcp/dhcpd.conf
# (add your comments here)
default-lease-time 600;
max-lease-time 7200;
option subnet-mask 255.255.255.0;
option broadcast-address 192.168.1.255;
option routers 192.168.1.254;
option domain-name-servers 192.168.1.1, 192.168.1.2;
option domain-name "mydomain.example";
subnet 192.168.1.0 netmask 255.255.255.0 {
range 192.168.1.10 192.168.1.100;
range 192.168.1.150 192.168.1.200;
}
$ sudo vim /etc/network/interfaces
auto wlan0
iface wlan0 inet static
address 192.168.3.1
netmask 255.255.255.0
up /sbin/iwconfig wlan0 mode TTTTTT && /sbin/iwconfig wlan0 enc
restricted && /sbin/iwconfig wlan0 key [Y] XXXXXXXX && /sbin/iwconfig
wlan0 essid test_wpa2
$ sudo vim /etc/default/isc-dhcp-server
INTERFACESv4="wlan0"
INTERFACESv6=""
$ sudo ifconfig wlan0 192.168.3.1 up
$ sudo service isc-dhcp-server stop
$ sudo service isc-dhcp-server start
$ sudo service isc-dhcp-server status
● isc-dhcp-server.service - ISC DHCP IPv4 server
Loaded: loaded (/lib/systemd/system/isc-dhcp-server.service;
enabled; vendor preset: enabled)
Active: active (running) since Sun 2022-01-09 12:24:33 IST; 5s ago
Docs: man:dhcpd(8)
Main PID: 50874 (dhcpd)
Tasks: 4 (limit: 9330)
Memory: 5.0M
CGroup: /system.slice/isc-dhcp-server.service
└─50874 dhcpd -user dhcpd -group dhcpd -f -4 -pf
/run/dhcp-server/dhcpd.pid -cf /etc/dhcp/dhcpd.conf wlan0
Jan 09 12:24:33 test dhcpd[50874]: PID file: /run/dhcp-server/dhcpd.pid
Jan 09 12:24:33 test dhcpd[50874]: Wrote 0 leases to leases file.
Jan 09 12:24:33 test sh[50874]: Wrote 0 leases to leases file.
Jan 09 12:24:33 test dhcpd[50874]: Listening on LPF/wlan0/02:00:00:00:00:00/192.168.3.0/24
Jan 09 12:24:33 test sh[50874]: Listening on LPF/wlan0/02:00:00:00:00:00/192.168.3.0/24
Jan 09 12:24:33 test sh[50874]: Sending on LPF/wlan0/02:00:00:00:00:00/192.168.3.0/24
Jan 09 12:24:33 test sh[50874]: Sending on Socket/fallback/fallback-net
Jan 09 12:24:33 test dhcpd[50874]: Sending on LPF/wlan0/02:00:00:00:00:00/192.168.3.0/24
Jan 09 12:24:33 test dhcpd[50874]: Sending on Socket/fallback/fallback-net
Jan 09 12:24:33 test dhcpd[50874]: Server starting service.
|
Step 16: STA : Ping AP |
Step 16: AP : Ping STA |
Note 192.168.3.1 is IP address of Access Point |
Note 192.168.3.10 is IP address of Station |
$ sudo ping 192.168.3.1
PING 192.168.3.1 (192.168.3.1) 56(84) bytes of data.
64 bytes from 192.168.3.1: icmp_seq=1 ttl=64 time=0.121 ms
64 bytes from 192.168.3.1: icmp_seq=2 ttl=64 time=0.091 ms
64 bytes from 192.168.3.1: icmp_seq=3 ttl=64 time=0.090 ms
64 bytes from 192.168.3.1: icmp_seq=4 ttl=64 time=0.097 ms
64 bytes from 192.168.3.1: icmp_seq=5 ttl=64 time=0.243 ms
|
$ sudo ping 192.168.3.10
PING 192.168.3.10 (192.168.3.10) 56(84) bytes of data.
64 bytes from 192.168.3.10: icmp_seq=1 ttl=64 time=0.092 ms
64 bytes from 192.168.3.10: icmp_seq=2 ttl=64 time=0.036 ms
64 bytes from 192.168.3.10: icmp_seq=3 ttl=64 time=0.094 ms
64 bytes from 192.168.3.10: icmp_seq=4 ttl=64 time=0.105 ms
64 bytes from 192.168.3.10: icmp_seq=5 ttl=64 time=0.094 ms
|
Step 17: STA : Run TCP server for TCP DL test |
Step 17: AP : Run TCP Client for TCP DL test |
$ sudo iperf -s -i 1
|
$ sudo iperf -c 192.168.3.10 -i 1 -t 30
|
Step 18: STA : Run TCP client for TCP UL test |
Step 18: AP : Run TCP Server for TCP UL test |
$ sudo iperf -c 192.168.3.1 -i 1 -t 30
|
$ sudo iperf -s -i 1
|
Step 19: STA : Run UDP server for UDP DL test |
Step 19: AP : Run UDP Client for UDP DL test |
$ sudo iperf -s -u -i 1
|
$ sudo iperf -c 192.168.3.10 -u -b 1000M -i 1 -t 30
|
Step 20: STA : Run UDP client for UDP UL test |
Step 20: AP : Run UDP Server for UDP UL test |
$ sudo iperf -c 192.168.3.1 -u -b 1000M -i 1 -t 30
|
$ sudo iperf -s -u -i 1
|